Captchas are annoying, painful innovations in tech let’s explore another way.
Captchas are using by 1000s of websites to prevent “bots” accessing the resource. They do a good job of preventing bots to access websites especially the image verification captchas
Captchas are using by 1000s of websites to prevent “bots” accessing the resource. They do a good job of preventing bots to access websites especially the image verification captchas, but they also do a good job at annoying honest users accessing websites. As computer technology as advancing, some bots are becoming so advanced that they can solve captchas faster and more accurately then even humans can, in fact, we ran a study and it was confirmed that on average computers have faster text recognition than humans.
Computer AI
As computer AI is advancing, I have been noticing a growing trend among the image captchas, they are becoming increasingly blurry and harder to solve. Image recognition software in most cases can solve or at least partially recognise the images better than humans. I was stunned one morning trying to access a website, it took me 4 tries just to get it right. It’s not just happening to be, just go on Reddit there are 1000s of people complaining. And rightly so, after 10+ years of IT innovation, we still can’t tell apart a bot from a normal user without a captcha.
Solution

I purpose a solution that has been talked about for many years now but has been very slow at being adopted.
Why not intentionally eat every visitor’s CPU cycles on entry to a website, we exhaust just enough so that an honest valid user wouldn’t notice because they are normal and won’t be making 1 million requests of spam a second unless they have like a million tabs open.
Spambots would be overwhelmed as they would be exhausting a lot more CPU Cycles and in turn, stop spamming as it wouldn’t be feasible.
Each time a client/user visits a website, the server should log the IP of the client and save it on the database, then send back a random piece of data to be hashed and a difficulty rating. The higher the difficulty the more CPU cycles will be required to come up with a solution.
Once the client/user has the data and difficulty, it would use SHA256 to hash the data with an additional nonce (a random piece of data) in a loop until “n” in leading zeros is discovered in the resulting hash. Where n is the difficulty. For example, if the difficulty is 2 then when the client hashes the data and random nonce value the resulting hash must lead by 2 zeros.
If a spam bot was to run 10000s of spams a second, the server would soon be too busy to send requests as they would be focusing on hashing solutions all day. And if for some reason the requests become too much by the spambots, the site master can just raise the difficulty.
Although hashing is taxing on the client by forcing them to loop through 1000s of hashes to find the correct one, the server will have a very fast time verifying, as the server only needs the nonce and hash to verify if it’s correct. It only needs to run 1 cycle to confirm this, since the nonce is already present.
Process of lawful access
- 1) Client sends request to server
- 2) Server sends random data that must be hashed to a specific difficulty
- 3) Client with use a random nonce alongside the data to hash 100s or 1000s of hashes to find one that matches the difficulty
- 4) Client finds a nonce that matches the difficulty and submits the request again with the attached hash and nonce
- 5) Server quickly verifies the nonce and hash is indeed correct and grants access to the resource.
Example code in python
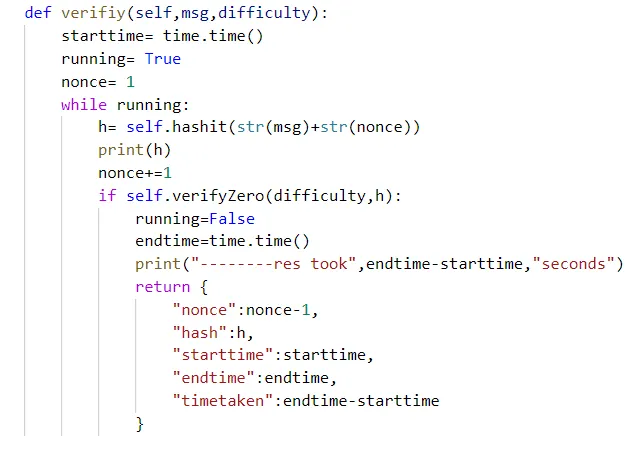
The verify function in python, takes a message and a difficulty rating, and returns the hash and nonce. It firstly sets the nonce=1 and starts a while loop. Within the loop the “hashit” function is called which takes a string and returns the sha256 hash in string. I attach the nonce to the msg and evaluate the hash returned by using the “VerifyZero” method which takes a difficulty and hash and checks if the leading number of zeros in the hash is equal to the difficulty, if yes return True and otherwise it returns false.
If the hash nonce matches the number of zeros (difficulty) then the while loop stops execution and the nonce and hash are returned.
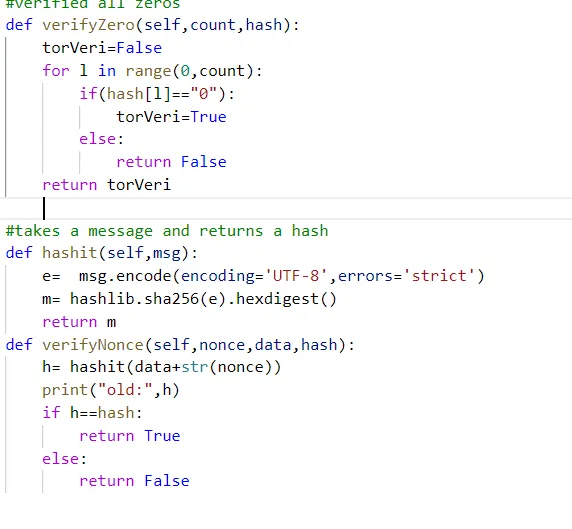
Helper Methods
The two helper methods I created are hashit which basically takes a message and returns a hash and secondly verifyZero which takes a difficulty and a hash to verify if there are (difficulty) number of leading zeros on the hash, it returns true if correct otherwise returns false